The 2026 Roadmap to Agile Architecture: Visual Planning, No-Code Backends, and Biometric Security

The 2026 Roadmap to Agile Architecture: Visual Planning, No-Code Backends, and Biometric Security
By Abo-Elmakarem Shohoud | Ailigent
 BEST METHODS AND TOOLS MENTIONED !
Source: Dev.to AI
BEST METHODS AND TOOLS MENTIONED !
Source: Dev.to AI
As we navigate the technological landscape of March 2026, the barrier between an idea and a fully functional enterprise system has never been thinner. In this era, where AI-driven automation is the standard rather than the exception, the role of the developer and the business owner has shifted from 'writing syntax' to 'architecting logic.'
At Ailigent, we have observed that the most successful digital transformations this year are not those that use the most complex code, but those that leverage rapid prototyping and ironclad security protocols. This tutorial will guide you through the 2026 standard for building a scalable, secure IT ecosystem from scratch.
Learning Objectives
By the end of this guide, you will be able to:
- Design a comprehensive visual sitemap to guide AI-assisted development.
- Deploy a robust, scalable backend using NocoBase 2.0 in a containerized environment.
- Implement WebAuthn in Node.js to replace vulnerable password systems with biometric security.
- Integrate these components into a cohesive automation strategy for your business.
Phase 1: The Blueprint - Visual Sitemapping for AI Alignment
Before a single line of code is generated or a database is provisioned, you must visualize the structure. In 2026, visual sitemapping is the primary 'prompt' we provide to our AI agents to ensure architectural integrity.
Visual Sitemapping is a methodology where hierarchical diagrams are used to represent the relationship between different pages, data entities, and user flows within a digital system.
Why Visual Planning Matters in 2026
With the rise of Agentic AI, the biggest risk is no longer 'buggy code' but 'architectural drift'—where an AI builds something that doesn't align with business logic. A visual sitemap serves as the source of truth. It allows stakeholders to identify bottlenecks in the user journey before they become expensive technical debt.
Exercise 1: The 'Logic-First' Flow Try mapping a simple HelpDesk system. Instead of thinking about 'buttons,' think about 'states.'
- State A: User submits a ticket.
- State B: Ticket is categorized (AI Automation).
- State C: Agent resolves ticket.
- State D: Dashboard updates in real-time.
Phase 2: Rapid Prototyping with NocoBase 2.0
Once the blueprint is ready, we need an engine. In 2026, we no longer spend weeks setting up CRUD (Create, Read, Update, Delete) operations. We use NocoBase.
No-code development is a paradigm where software is built using graphical interfaces and configuration rather than traditional manual programming, significantly reducing time-to-market.
Step-by-Step: Deploying NocoBase with Docker
To build our HelpDesk system, we will use NocoBase 2.0. This version is particularly powerful for its 'Collections' engine which handles complex relationships effortlessly.
- Environment Setup: Ensure your 2026 cloud instance has Docker and Docker Compose installed.
- Deployment Command:
docker-compose up -d - Data Modeling: Within the NocoBase UI, create two tables:
TicketsandCategories. Link them with a 'Many-to-One' relationship. - Access Control: Define roles for 'Customers' and 'Support Agents.'
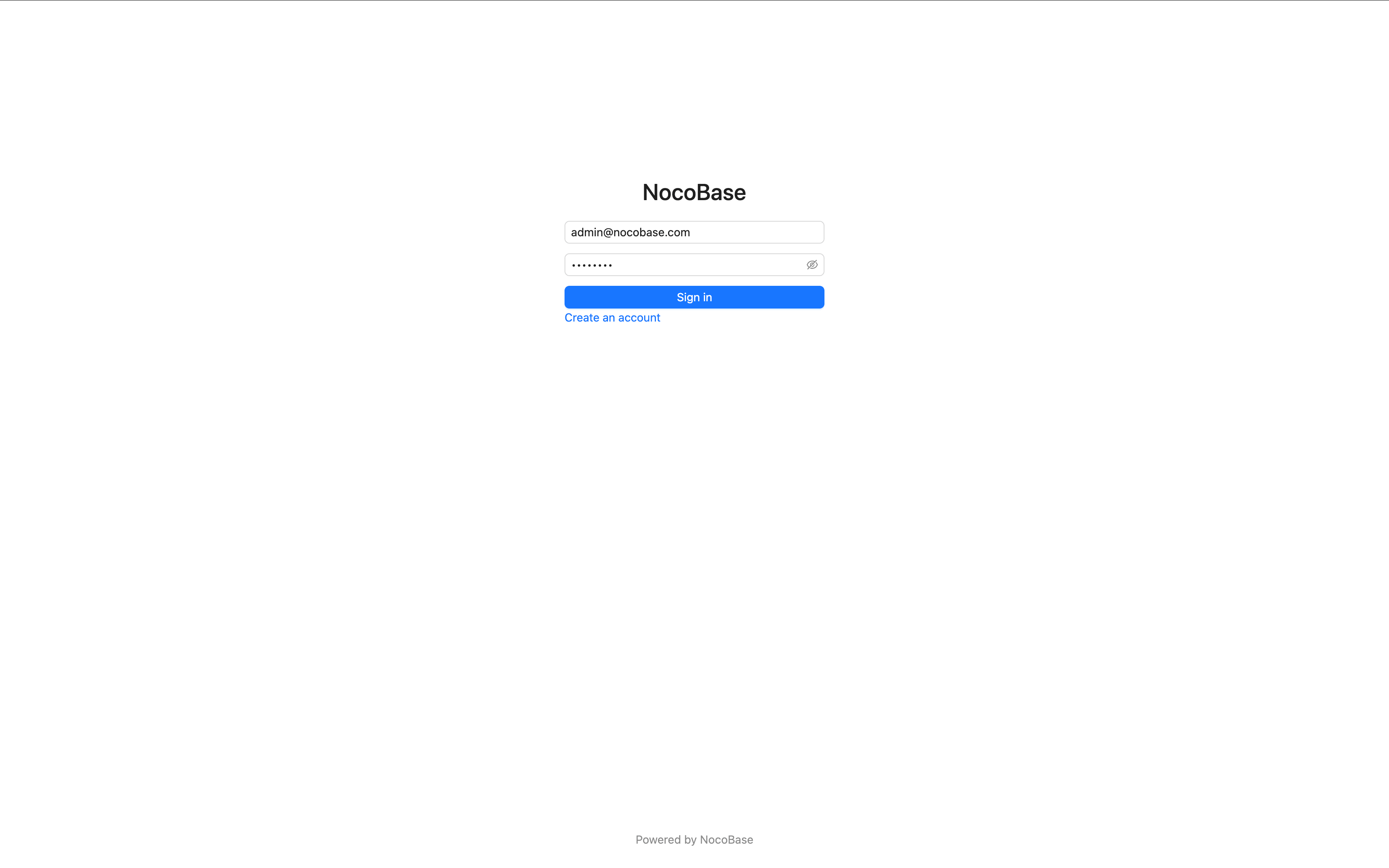 NocoBase 2.0 Beginner Tutorial - Chapter 1: Getting Started
Source: Dev.to AI
NocoBase 2.0 Beginner Tutorial - Chapter 1: Getting Started
Source: Dev.to AI
Abo-Elmakarem Shohoud often emphasizes that the value of NocoBase lies in its extensibility. Unlike closed-source platforms of the past, NocoBase 2.0 allows you to inject custom logic when your business outgrows the standard features.
Comparison of Development Approaches in 2026
| Feature | Custom Code (Node/Python) | Low-Code (Retool/OutSystems) | No-Code (NocoBase 2.0) |
|---|---|---|---|
| Speed to MVP | Slow (Weeks) | Medium (Days) | Ultra-Fast (Hours) |
| Maintenance | High (Manual) | Medium | Low (Automated) |
| Security | Developer-dependent | Platform-dependent | Enterprise-grade (Native) |
| Best For | Unique Algorithms | Internal Tools | Business Process Automation |
Phase 3: Hardening the Perimeter with WebAuthn
As AI-driven phishing attacks have become more sophisticated in 2026, traditional JWT (JSON Web Tokens) and passwords are no longer sufficient for high-stakes business data. This is where WebAuthn becomes mandatory.
WebAuthn (Web Authentication) is a global standard for authenticating users on the web using public-key cryptography and hardware-based authenticators (like FaceID, TouchID, or YubiKeys).
The Problem with Bearer Tokens
In the past (2024-2025), we relied heavily on bearer tokens. However, a stolen token in 2026 can be used by an AI bot to impersonate a user perfectly. WebAuthn solves this by proving possession of a physical device or biometric signature.
Implementing WebAuthn in Node.js (Simplified Logic)
To secure your NocoBase backend or any custom Node.js application, follow this flow:
- Registration: The server sends a 'Challenge' to the client. The client signs it with a private key (stored in the device's Secure Enclave) and sends the public key back to the server.
- Authentication: When the user logs in, the server sends a new challenge. The user 'signs' it with their fingerprint/face. The server verifies this signature against the stored public key.
Code Snippet: The Server-Side Challenge
const { generateRegistrationOptions } = require('@simplewebauthn/server');
// 2026 Standard Security Implementation
const options = await generateRegistrationOptions({
rpName: 'Ailigent Secure Portal',
rpID: 'ailigent.ai',
userID: user.id,
userName: user.email,
attestationType: 'direct',
authenticatorSelection: {
residentKey: 'required',
userVerification: 'preferred',
},
});
Phase 4: Scaling with Ailigent Automation
Building the system is only half the battle. In 2026, the real competitive advantage comes from how these systems talk to each other. By integrating your NocoBase backend with AI agents managed by Ailigent, you can automate:
- Sentiment Analysis: Automatically prioritize tickets where the customer is frustrated.
- Predictive Maintenance: Use historical data to resolve issues before the user even reports them.
- Biometric Auditing: Ensure that sensitive database changes are only made after a WebAuthn-verified biometric check.
Try It Yourself: The 5-Minute Challenge
- Go to a visual mapping tool (like FigJam or Miro).
- Map out a 'Lead Generation' flow.
- Identify where a 'Password' can be replaced by a 'Biometric Scan'.
- Ask yourself: "If I had to scale this to 10,000 users tomorrow, where would it break?"
Key Takeaways
- Architecture Over Syntax: In 2026, spending time on visual sitemaps saves hundreds of hours in AI-assisted development.
- No-Code is Enterprise-Ready: Tools like NocoBase 2.0 provide the speed of no-code with the reliability of a containerized SQL backend.
- Biometrics are Non-Negotiable: Move away from passwords and standard JWTs toward WebAuthn to protect your business from 2026-era automated threats.
- Start Small, Scale Fast: Use Docker to deploy your infrastructure, ensuring portability across any cloud provider.
Next Steps
- Explore the NocoBase Documentation for advanced collection configurations.
- Review the WebAuthn Guide to understand the underlying cryptography.
- Contact Abo-Elmakarem Shohoud at Ailigent to audit your current automation stack for 2026 readiness.
Bottom Line
The future of business automation isn't about working harder; it's about building smarter, more secure frameworks that allow AI to do the heavy lifting while you focus on strategy.